Net Neutrality: The Wire Does Not Dictate Its Use
The wire that brings electricity to your home does not dictate when you can turn your lights on. It does not decide whether you may use a washing machine or microwave. It does not determine which appliance manufacturers’ products you can use.
Imagine the world if it did:
You only subscribe to the electric company’s “basic” package, so you’re not allowed luxury devices like a Breville tea maker or a Juicero connected juicer (in this case your electric company may inadvertently be doing you a favor) - you get one washing machine, one dryer, an iron and a coffee maker. There’s a rumor they may add dishwashers to the basic package but for now you have to buy a mid-tier package to be allowed to use them. You get power one television, not larger than 35” and only HDTV, not 4K.
If you want to power an exercise bicycle, sonic toothbrush or your great uncle’s iron lung you’ll need the “Health & Fitness” package. Induction burners and sous vide cookers need the “Foodie” package, which is on sale now when you bundle it with three other popular packages, though watch out for the hidden fees that kick in after the first year; they’ll really get you where it hurts.
You used to be able to use Samsung appliances at home but now you’ll probably to have to replace them because your electric company switched its marketing alliance from Samsung to GE and is no longer allowing Samsung appliances to be powered during the daytime. And your kids are really upset because Disney was part of the Samsung alliance, and the electric company won’t allow you to play Disney movies on your non-4K TV.
This is the world you might live in if your power company managed your electric service the way cable companies manage television service.
Of course, this is insane. Nobody in their right mind would possibly suggest this. The wire does not dictate its use.
Let’s take a quick, high level look at why it’s important that the wire that connects you to the Internet is neutral to what it carries.
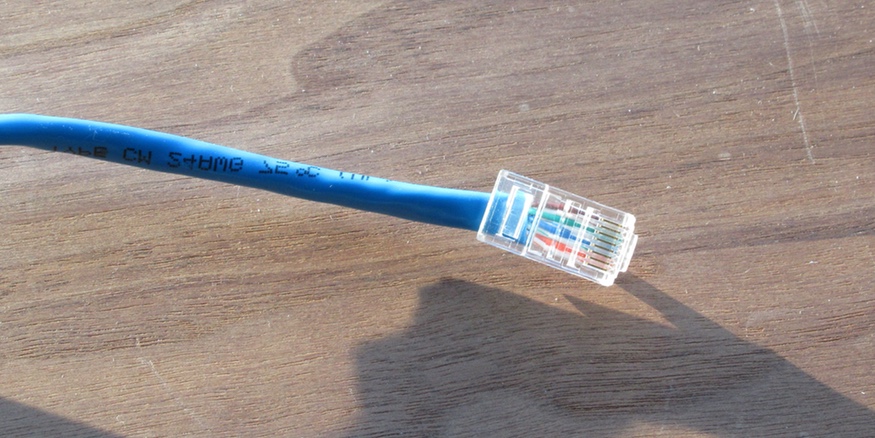
The Wire and The Internet Architecture
The Internet is built using a technology stack - each layer builds on layers below it. Each supporting layer provides an abstract view of the network and treats anything above it as opaque.
Let’s start with HTTP - even if you’re not a techie, you’ll certainly have typed “http:” into your web browser many times. HTTP provides an abstract view of a network of documents. While the documents link to one another and are provided in a variety of formats, HTTP makes no assumptions about their content or how to handle them or process them - it only provides a mechanism for manipulating them as opaque objects - transfer them, delete them, update them. The browser will act on their contents and invoke HTTP again as it needs to.
HTTP almost always runs over TCP, the Transmission Control Protocol. TCP is one of the most important, fundamental parts of the Internet protocol stack. It provides an abstract view of the network as a reliable stream of bytes. This abstraction is very limited - TCP lets you know that the data you send gets to its recipient - exactly once, in the order you sent, unmodified. It attempts to do so efficiently but does nothing more. Email, the web, remote login, screen sharing, file sharing, even audio and video streaming are all built over TCP. TCP makes no assumptions about the traffic it carries.
TCP is built atop an even more fundamental protocol - IP, the Internet Protocol. IP provides a uniform abstract view of a low level network where communications are broken into packets and provides a uniform scheme for naming (addressing) each computer on the Internet independent of varying types of hardware addresses they may have. Like TCP, IP does the bare minimum necessary to provide the abstract view of the network that it offers.
And, importantly, IP makes no assumptions about the data it carries. It simply provides this abstract view of the network and attempts to deliver packets.
What’s below IP? That’s where the wild things are… these are the different kinds of network technologies that IP insulates the upper layers from. Ethernet, cellular, satellite, packet radio, Bluetooth, PPP over (cough) modems and serial lines, possibly even token ring or ATM and other, outdated network technologies.
Technically, the service that an Internet Service Provider provides is the network layer link. They take IP packets which contain who knows what - IP certainly is not allowed to care - and transport them from the boundary of the customer’s network to the next hop along their journey. To do this, they operate networking hardware such as cable or satellite or cellular and they operate IP routers, which interpret the IP layer and decide what to do next with packets.
The ISP has one job - they’re the wire. And the wire does not dictate its use.
Any attempt by them to inspect the higher layers - which determine the service the customer is trying to use - blatantly violates the architecture of the Internet protocols - blatantly violates the architecture of the Internet itself - and opens it up to a world of pain and unreliability.
For your ISP to manage your Internet connection as horribly as your cable company manages its television service, it has to be able to determine what you’re trying to do over your Internet connection.
Because we design the lower layers to be blind to what they’re carrying, there are no reliable mechanisms for inspecting the payload and reliably identifying what service is being used or application is being run. Yes, you can tell that web pages are being fetched, but you may not be able to reliably tell that they’re from Facebook.
Upper layers may also be encrypted, obscuring information. For medium to large companies it may be impossible to correlate the service with the computers providing it. Computer addresses and names can change rapidly as servers come online and go offline. Businesses often use “content distribution networks”, which serve content more quickly to customers, and a CDN server can easily handle multiple businesses. Do you have any idea what business is using “ec2-34-196-7-251.compute-1.amazonaws.com”? Me neither, but my computer just talked to that server.
The opacity of data being carried by TCP and IP makes it difficult to classify Internet traffic. And as more and more Internet traffic is encrypted, it becomes more and more difficult to inspect it and reliably classify it.
Making Security Not Secure
It is technically feasible to break HTTPS encryption. If you can create a globally recognized top level encryption certificate you can then forge a certificate for the destination, intercept encrypted communications, inspect them and then relay them (and possibly tamper with them) to their intended destination - the “man in the middle” attack. It’s certainly believable that companies like AT&T, Verizon and Comcast can place top level certificates that would allow them to do this.
If you’re going to suggest that it’s okay for ISPs to break the SSL/TLS layer which protects encrypted HTTP and email, think about that for a moment. Why do we encrypt these communications? They contain phone numbers, social security numbers, credit card numbers, baby camera video, people’s locations, photos, and other personal and intimate information. Are you seriously going to suggest that the country’s most hated businesses - businesses which routinely break promises to customers and defraud them with hidden fees - should just be trusted to open everyone’s private communications and just do the right thing by their customers?
Even if you break encryption it’s still difficult to reliably classify and categorize traffic. But think about the business proposition for the ISPs - do they really need to reliably classify traffic? Or do they just need to make things inconvenient and annoying enough for you that you’ll pay extra to be able to work from home or watch Netflix?
Security And Network Neutrality
The Internet is often used for security-related applications. These may be physical security, like a camera near your door or proximity sensors. It may be computer security, getting antivirus updates and malware protection. Or it may involve securing the Internet itself.
If your security-related devices are suddenly throttled, limited, delayed or not allowed to talk to their servers, what happens to them? How much less reliable will they be, or will they continue to work at all?
If you think Internet of Things security is a mess now, just wait till ISPs start interfering with the parts of it that did work.
FCC: Hey, The Internet Doesn’t Really Matter, Let The ISPs Have Their Way
I’m sure that you’re aware that the FCC is voting on December 14, 2017 to end network neutrality rules. Which, of course, is the reason I’m writing this. All major Internet industry companies that aren’t ISPs are strongly opposed to repealing these rules. The voting public is also strongly opposed. And yet the current management of the FCC seems dead set on the repeal.
Since its origin in the 1970s, the Internet has transformed the way we communicate. We can reach people on the other side of the globe in seconds. Who needs video phones? We can video chat with groups of people any time we want. We can share files,
It works. It works fantastically well. The abstraction of the technology stack - providing a minimal, useful abstract view of the underlying network and being blind to what’s being done with it - is the beating heart of the Internet architecture. This works so well that we’ve put connected billions of devices using technology that’s over 40 years old that the entire world depends on every second of every day.
The Internet connects governments, businesses, individuals, non-profits, devices, schools, military organizations,banks, laboratories to one another. For many businesses the Internet is like oxygen is to humans. The variety of things that use the Internet is stunning and it’s ability to make that work boils down to the simple architectural principle of the network being neutrality to what it’s carrying.
So What If They Screw Up The Internet, That Doesn’t Really Affect Me
You almost certainly depend on the Internet, even if you don’t think so.
Your city or town government depends on it. They manage services, collect taxes, share information and schedules using the Internet.
Your doctor uses it to research medical conditions, keep up to date on medications and treatments, access medical records and communicate with other doctors, hospitals and pharmacies.
Your favorite sports teams use it to organize travel, sell tickets, and distribute information about games and schedules and players.
Your church uses it to share information and schedules and to communicate with other churches and church-goers.
Your favorite musicians use it to produce and distribute music, organize tours and keep in touch with fans.
Your kids’ schools use it to communicate with teachers, bus drivers, their administration and other schools. Substitute daycare or whatever activities your kids are involved in.
Have a smart phone? Use any apps on it? Keep photos or documents “in the cloud”? Watch Netflix or Amazon Prime Video? You’re using the Internet.
It’s likely that you use the Internet even if you don’t think you do. And even if you don’t, you almost certainly depend on people who depend on it. And the reason it works is that the wire doesn’t dictate what you do with it - and the network is neutral to the application using it. Without that, the Internet itself is in danger.
Okay, What Should I Do?
You can let the FCC know how you feel but it’s late for that, and it looks like the FCC really doesn’t care.
You can support the Electronic Frontier Foundation.
You can take every opportunity to let your Internet Service Providers know that you want them to stay neutral.
You can encourage your local town, city or state to negotiate net neutrality into the service contracts they have with ISPs.
You can contact your representatives in Congress to demand they protect the Internet.
For more information:
Github: Save net neutrality in the US—again
EFF: Net Neutrality
Reddit: Net Neutrality