Security, Privacy and IoT: The Week of March 6th, 2017
Security
The biggest story in security this week is Wikileaks’ dump of CIA documents, reminding people that yes, the CIA is a spy agency and that yes, spy agencies would want to have cracking tools.
The big takeaways are that they have tools for hacking specific devices. Wikileaks spun this as the CIA being able to crack Signal and Whatsapp, but nothing in the documents indicates that - it’s more that the CIA can take control of the phone’s or computer’s OS - once that’s done, they can compromise any app without breaking its protocol.
Wired has a few non-technical articles running it down:
https://www.wired.com/2017/03/wikileaks-cia-hacks-dump/
https://www.wired.com/2017/03/worried-cia-hacked-samsung-tv-heres-tell/
https://www.wired.com/2017/03/cia-can-hack-phone-pc-tv-says-wikileaks/
Apple is on the ball saying most of the iOS vulnerabilities disclosed are fixed:
Google, too:
If you’re freaked out about the CIA dump, here’s a good perspective on it:
Meanwhile, Western Digital’s My Cloud networked hard drive has some holes:
https://www.engadget.com/2017/03/05/wd-my-cloud-security-exploits/
Wordpress released a security update. You should be applying Wordpress updates automatically; if you’re not, upgrade ASAP.
https://wordpress.org/news/2017/03/wordpress-4-7-3-security-and-maintenance-release/
Another dump this week that promised over a billion “identities” was a dump of a database used by spammers. This database correlated user identities (emails, names), physical addresses and IP addresses. The latter bit has particularly interesting privacy implications. You can’t pinpoint a person by their IP address as one IP address usually hides a home or office behind it, with multiple people using it. Still,
https://mackeeper.com/blog/post/339-spammergate-the-fall-of-an-empire
The DoJ makes its priorities known by dropping a child porn case in order to avoid disclosing how they cracked a device:
You know all those annoying “Captcha” forms that sites use to protect themselves against automated access? “Click this box to prove you’re a human”, “Select all the pictures with a three-eyed cat in them” - Google has developed a background version that doesn’t require human interaction.
https://arstechnica.com/gadgets/2017/03/googles-recaptcha-announces-invisible-background-captchas/
Privacy
The US Senate is trying to make sure that the FCC doesn’t require ISPs to protect your personal data in the future. Because what’s awesome for US citizens? Having their Internet service providers snoop on their online activity and sell that information to unregulated third parties.
http://boingboing.net/2017/03/09/selling-your-kids-data.html
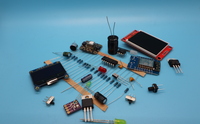
IoT
Nest has added two factor authentication:
https://www.engadget.com/2017/03/07/nest-two-factor-authentication/
Ring doorbells send packets to China. Block outgoing traffic from them to 106.13.0.0:
https://www.reddit.com/r/homeautomation/comments/5xa0h1/ring_pro_doorbell_calling_china/
Power consumption is the single biggest limitation of mobile devices. We can throw more computing power in them but we can’t power it for very long. MIT has developed a new chip that lets devices process voice at a fraction of the power they currently need.
https://www.wired.com/2017/03/mit-microsystems-technology-lab-voice-chip/
And The Onion has the last word related to the CIA document dump:
http://www.theonion.com/article/samsung-smart-tv-owner-learning-about-majority-fea-55493