Security, Privacy and IoT: The Week of February 27th, 2017
Security
If you want a phone that’s less likely to be broken into simply because it does much less, the Nokia 3310 may be for you. No App Store and no wifi reduce its attack surface to whatever vulnerabilities are built into Nokia’s software and its baseband firmware.
Google disclosed an unpatched vulnerability in Microsoft’s Internet Explorer and Edge browsers which allows an attacker to execute arbitrary code, after reporting it to Microsoft 90 days ago with no patch forthcoming. https://arstechnica.com/security/2017/02/high-severity-vulnerability-in-edgeie-is-third-unpatched-msft-bug-this-month/
A severe bug in the popular Wordpress plugin NextGEN Gallery allows attackers to execute arbitrary SQL code. Keep your Wordpress installs and plugins up to date!
Slack disclosed a vulnerability in its web app which allowed an attacker access to other users’ authentication tokens (and therefore their Slack accounts). Fortunately there’s no sign that this was ever exploited.
https://www.wired.com/2017/03/hack-brief-slack-bug-everyones-worst-office-nightmare/
Wired has a lightweight non-technical overview of the security mess that awaits the world with connected medical devices.
https://www.wired.com/2017/03/medical-devices-next-security-nightmare/
And Trojan malware has a novel way of receiving commands - via the DNS. Covert communication channels that masquerade or are carried over infrastructure protocols like DNS are a great way to control and communicate with malware.
USB controllers in your computer run their own firmware, which has its own vulnerabilities - independent of the software and OS your computer runs. This firmware may become compromised by malicious USB devices. There is now a USB firewall - plug an untrusted USB device into it and plug it into your computer. The firewall inspects all USB taffic and protects your computer’s USB firmware from malicious requests. Unfortunately, the current version can only run at 12Mbps.
https://github.com/robertfisk/USG/wiki
Privacy
This one belongs under both Privacy and IoT: a children’s connected teddy bear was compromised, leaking 800,000 accounts and held ransom by attackers. Oh, and millions of voice messages were also leaked.
The latest Yahoo hack is now bad for Yahoo executives, too.
The FCC has not got your back when it comes to protecting your privacy online. https://www.wired.com/2017/03/fcc-graciously-sets-internet-providers-free-sell-data/
IoT
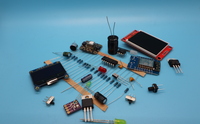
The Raspberry Pi Zero W - a Raspberry Pi Zero with Wifi and Bluetooth - will be available soon, giving us a new way to embed a little Linux in everything.
https://www.raspberrypi.org/blog/raspberry-pi-zero-w-joins-family/
The Withings brand will vanish as the company is absorbed by its new owner, Nokia. Withings delivered some of the earlier connected devices, like scales and blood pressure cuffs.
https://techcrunch.com/2017/02/26/goodbye-withings-hello-nokia/
Amazon’s Alexa gets even wider distribution as Motorola decides to bake it into their new smart phones as their voice assistant.
https://techcrunch.com/2017/02/26/motorola-picks-amazons-alexa-as-its-voice-assistant/