Password Dumps: How To Protect Yourself
By now you’re probably used to reading about web sites getting broken into, exposing millions of accounts.
The information that crackers get varies… they may get email addresses and encrypted passwords. It may be your IP address, name, plain text password, credit card information, social security number… it all depends on what the site collects and how they secure it.
This time around Adult Friend Finder was breached, exposing 340 million accounts as well about another 73 million accounts on other sex-related sites.
What do people do with these things?
User account information is valuable.
Spammers buy email addresses for mailing lists.
Crackers buy mail address/username/password combinations to break into systems.
And identity thieves like to get ahold of other information - social security numbers, phone numbers, addresses, birthdates.
For sex-related sites like Adult Friend Finder, you can imagine that finding accounts belonging to celebrities, politicians or other public figures could be very interesting.
Old accounts linger
You may think to yourself “but I had an account 17 years ago… it can’t possibly still be there”. Leaked Source indicates that user accounts go back 20 years.
Web sites don’t have a lot of incentive to prune old accounts. Your privacy and security are rarely their top priority. Storage is cheap and database maintenance is not… so expect that when you sign up for an account somewhere that it will persist as long as the site does, and possibly longer.
Your deleted account may also still exist
Leaked Source, who reported the Adult Friend Finder breach, also reports that the database included almost 16 million “deleted” accounts. Be aware that deleting your account is no guarantee that it will be purged from the system. Your account information and activity may well remain in the system and will almost certainly remain in backups.
Users: How to protect yourself
- Assume your password is not protected - use different, strong passwords for every web site you use. I cannot overstate how important this is. Use a password manager like 1Password to help you manage your passwords. And you’re probably safe letting Safari or Chrome memorize and sync your passwords - as long as you keep your Apple and Google accounts secure (use 2 factor security on them - another thing I cannot overstate).
- Treat personal security questions (“What is the name of your favorite teacher?”) like passwords - assume any answers to personal security questions are not protected.
- Don’t give the site more real information about yourself than it absolutely needs. Most sites are not doing credit or background checks on you. It’s often fine to lie about your name, birthday, address.
- Don’t depend on a site living up to its privacy policy or promises about account security. It’s great that a site has a privacy policy, and users should hold the site to it. However, it may fail to live up to the policy either accidentally (bugs in the software may allow your personal information to leak in ways they promised it wouldn’t) or intentionally (the site’s management simply decides to say one thing and do another). And privacy policies sometimes do not survive business acquisitions, so if the site is acquired by another company the new owners may not honor the old policies.
- Sign up for a password breach notification service. Leaked Source operates one. You might also try Have I Been Pwned?, which allows you to search for your email address through account dumps that they have access to.
If you feel it might be damaging to you (personally, professionally) if your use of the site is revealed, you may want to take further steps to protect yourself:
- Set up and use an anonymous email address which you use only for this site.
- Many sites record your IP address, which identifies your computer on the Internet. Consider using a VPN like Witopia to mask your IP address.
- If you have to pay to use the site, buy a rechargeable or pre-paid Visa card and use it without associating your name or personal information with the card.
- Browse the site in private browsing mode with browser extensions disabled - browser extensions can leak site usage details, and private browsing mode will help ensure that the site can’t save information that might cause it to start popping up in ads on other sites (the way that looking at an item on a shopping site will often cause that item to start showing up in ads on Facebook).
Your situation and level of concern will have to dictate how far you go with these steps - you might for instance pay for the VPN using a prepaid card as well.
Developers: How to protect your users
- Hire or contract with a security-knowledgable devops person. Your system needs to have security designed into it, not added on later. Unless you have truly security savvy developers or designers in house, design consultations with a security expert can protect both your users and your own business and save you from expensive software overhauls later (as well as a lot of negative press when a cracker dumps your user accounts on the Internet).
- Perform regular security audits and penetration testing. Automate this as much as possible.
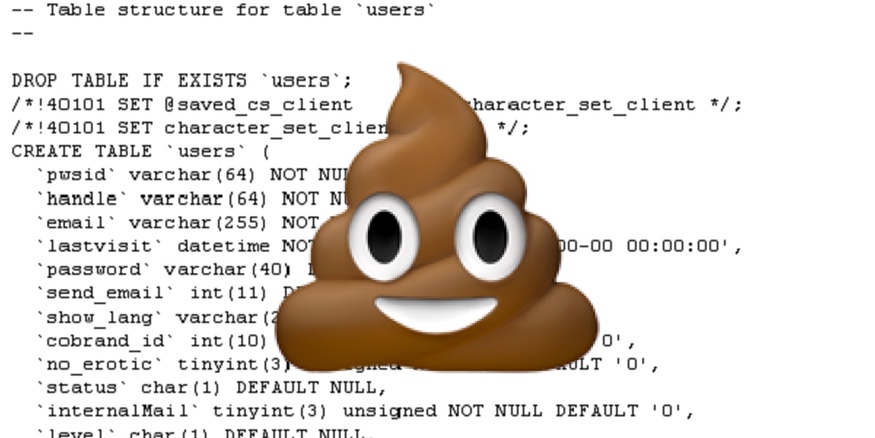
- Protect sensitive information like passwords by encrypting it properly. Never store passwords in plain text.
- Encrypt all network connections. If you use HTTP, use HTTPS - for everything.
- Isolate your account server from the server that runs your main application. Your account server will usually be the primary target for attackers. The less it does the harder it will be to break into. Isolating the servers helps mitigates the damage from a break-in.
- Do not collect any more information about the user than you actually need. For instance, if you never use their address for anything then don’t ask them for it.
- Regularly remove old account information and user data from your database. If you need to keep old records for research or marketing purposes, migrate them to a secure database that is isolated from the public Internet.
- Have a clear privacy policy and adhere to it.